My journey into service meshes began on April 27, 2020 when I was selected to be a mentee under the banner of Community Bridge for the Summer of 2020. The Community Bridge Mentorship is a structured remote learning opportunity for aspiring open source software developers. The projects they host are mentored by experienced open source project developers and maintainers.
Stumbling into Service Mesh Interface (SMI)
I began working on SMI Conformance testing under the guidance of Lee Calcote, Founder of Layer5, in February 2020. Since then, my path into the world of service meshes has brought me an avalanche of opportunities and has helped me grow by leaps and bounds as a developer. The Service Mesh Interface (SMI) is a standard interface that encapsulates various common service mesh functionalities. It explains several Custom Resource Definitions (CRDs), their configuration variables, and their corresponding effect on the service mesh underneath in full detail. What makes SMI vital is that these CRDs are generic, and the specifications are implemented and actively followed up by various service meshes. Some of these service meshes have developed adapters that define SMI CRDs as a wrapper over the APIs they already provide, instead of adhering to the SMI spec internally. SMI specifications address essential features for the most common service mesh use cases:

- Traffic policy – To apply policies like identity and transport encryption across services
- Traffic telemetry – To capture key metrics like error rate and latency between services
- Traffic management – To shift traffic between different services
However, at the moment, no service meshes adhere to the SMI specifications completely. Service meshes are rapidly developing and making active efforts to extend their feature set. Simultaneously, SMI has also been working towards adding more features to its specifications.
Consequently, it becomes a necessity for continual validation of service mesh conformance with respect to SMI specifications and the various versions of those specifications. The process of verifying conformance needs to be standardized and tooling made available. Hence, our project efforts to create an SMI conformance tool.
Meshery to the Rescue
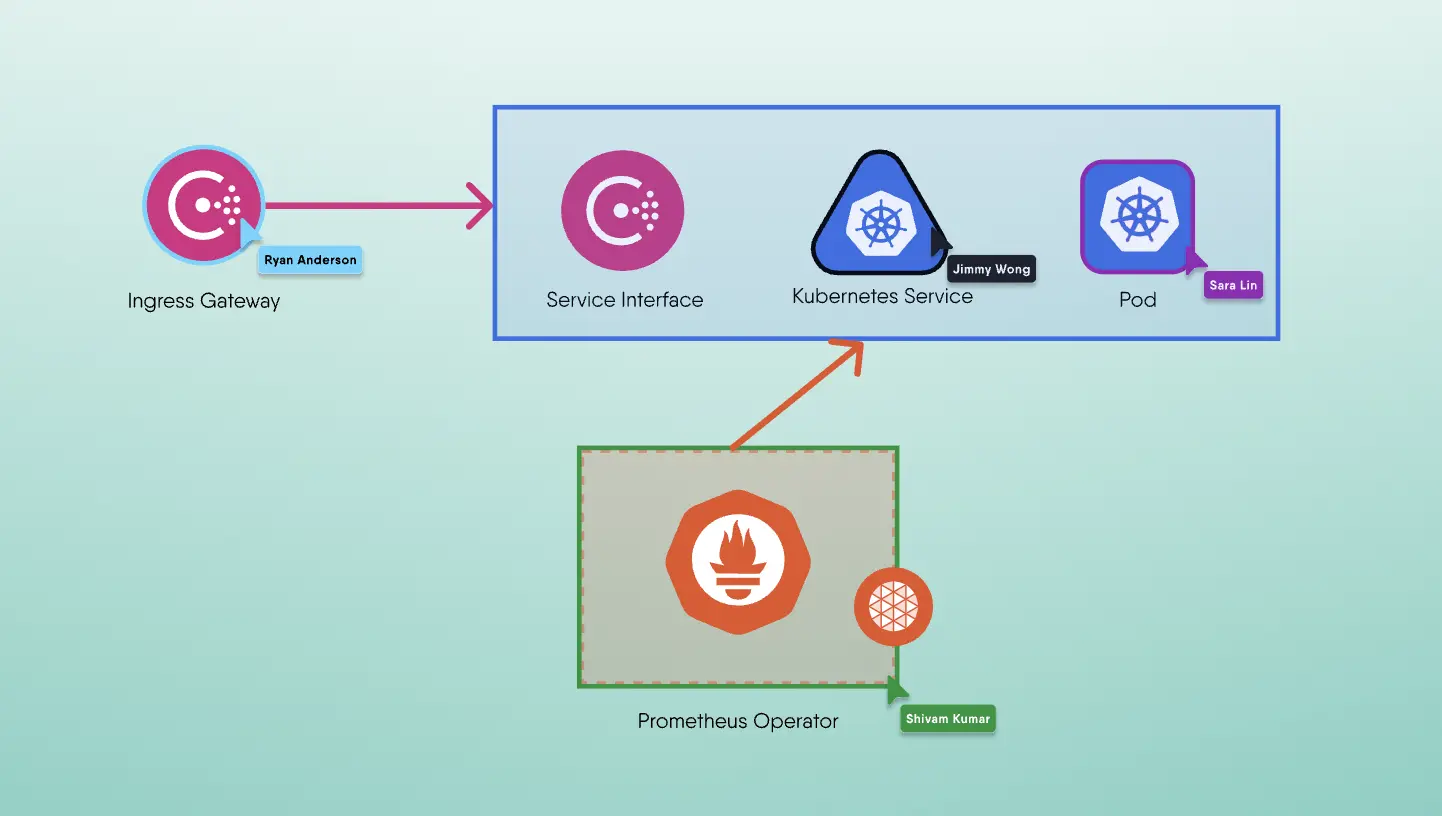
Meshery is the multi-service mesh management plane, offering lifecycle, configuration, and performance management of service meshes and their workloads. It is closely connected to the Kubernetes cluster and allows easy deployment of various service meshes and sample applications onto those meshes. Meshery enables operators to run performance tests on workloads, collect, store, and manage the test results.
We had found our solution. By leveraging the features provided in Meshery, we would be able to focus on the conformance validation and testing instead of sweating over the complexity in deployments. We can also use the performance management infrastructure to manage the conformance tests and their results. And so, the tool will be developed as an integral part of Meshery to aid and abate SMI conformance woes. We are now enhancing Meshery to automate the process of verifying conformance against a standard set of tests against a sample workload designed specifically for SMI conformance testing. By the time we’re through, this capability of Meshery will allow each project to validate its conformance to each version of the SMI specifications and will provide a detailed report.
My Projects
The goals accomplished in my tenure at Layer5 are summarized as follows:
- Meshery Providers - Ported Meshery and its remote provider from using session based authentication to JWT based auth. This opened doors to:
- Usage of refresh tokens for longevity of sessions instead of asking user to re-login frequently.
- CLI based authentication (not done yet, but is on the roadmap)
- Image Hub - WASM based envoy network packet filters in Rust-lang. Built a demo app demonstrating its potentials; we also built a WASM filter which performs custom user specific rate limiting. This app was demo’ed in Dockercon 2020 under the header “Service Meshing with Docker Desktop and WebAssembly”.
- Implementing the Service Mesh Performance Specification - Enhanced Meshery’s performance testing and profile management capabilities. Added support for customizing the requests made by the load generator, and added the capability of using performance test profiles in the tool.
You can find my code in the Learn Layer5 repository.
Love for the Community
I have been actively involved in the Layer5 community for a number of months now and am proud of the contributions I have made to various projects under the Layer5 banner. The Layer5 community represents an eclectic mix of geeky developers, out of the box thinkers, sassy writers and some of the most amazing people I have met so far in the open source community. We build projects to provide learning environments, deployment, and operational best practices, performance benchmarks, create documentation, and more. I am truly ecstatic to be a part of such an enthusiastic and welcoming community.
As you’ve made it to the end of my post, why not stick around and take a look at the amazing projects I just described? You might just find your dream project and if not, I can promise that you will at least end up becoming a part of one of the best open source communities out there.
To stay tuned with the progress of the project, please join us in the Slack channel!