Service Mesh: Istio
Microservice architectures offer some solutions while posing new ones. Application division into separate services makes scaling, updating, and development easier. It also provides you with a lot more moving pieces to connect and secure. It can get quite complicated to manage all of the network services, including load balancing, traffic management, authentication and authorisation, etc.
Istio, an open-source service mesh created by Google, IBM, and Lyft, enables you to connect, monitor, and secure microservices that are hosted on-premises, in the cloud, or with orchestration systems like Kubernetes and Mesos. The beta version of Istio was announced in the year 2018 in KubeCon on Google Cloud.
Before moving on to what Istio is and how it works, let us look into what service meshes are and why there was an urgent need for them as microservices started getting used more.
Service Mesh
A service mesh is an infrastructural layer that is used to provide secure communication between different services for on-prem, cloud or multi-cloud infrastructure. It allows us to add features like observability, traffic management, and security without having to add that to our code. The term "service mesh" refers to both the kind of software you employ to carry out this pattern and the security or network domain that results from its application.
Service meshes are divided into two parts: the control plane and the data plane. The control plane's responsibilities include securing the mesh, facilitating service discovery, doing regular health checks, enforcing policies, and handling other operational issues. A central registration of services and their corresponding IP addresses is referred to as service discovery. To share with other services how to communicate with it and to assist enforce rules on which services are allowed to communicate with which other services, the application must be registered on the control plane.
The communication between services, on the other hand, is handled by the data plane. Because many service mesh solutions use a sidecar proxy to manage data plane connections, the amount of knowledge that the services must have about the network environment is constrained.
Inside the Istio service mesh
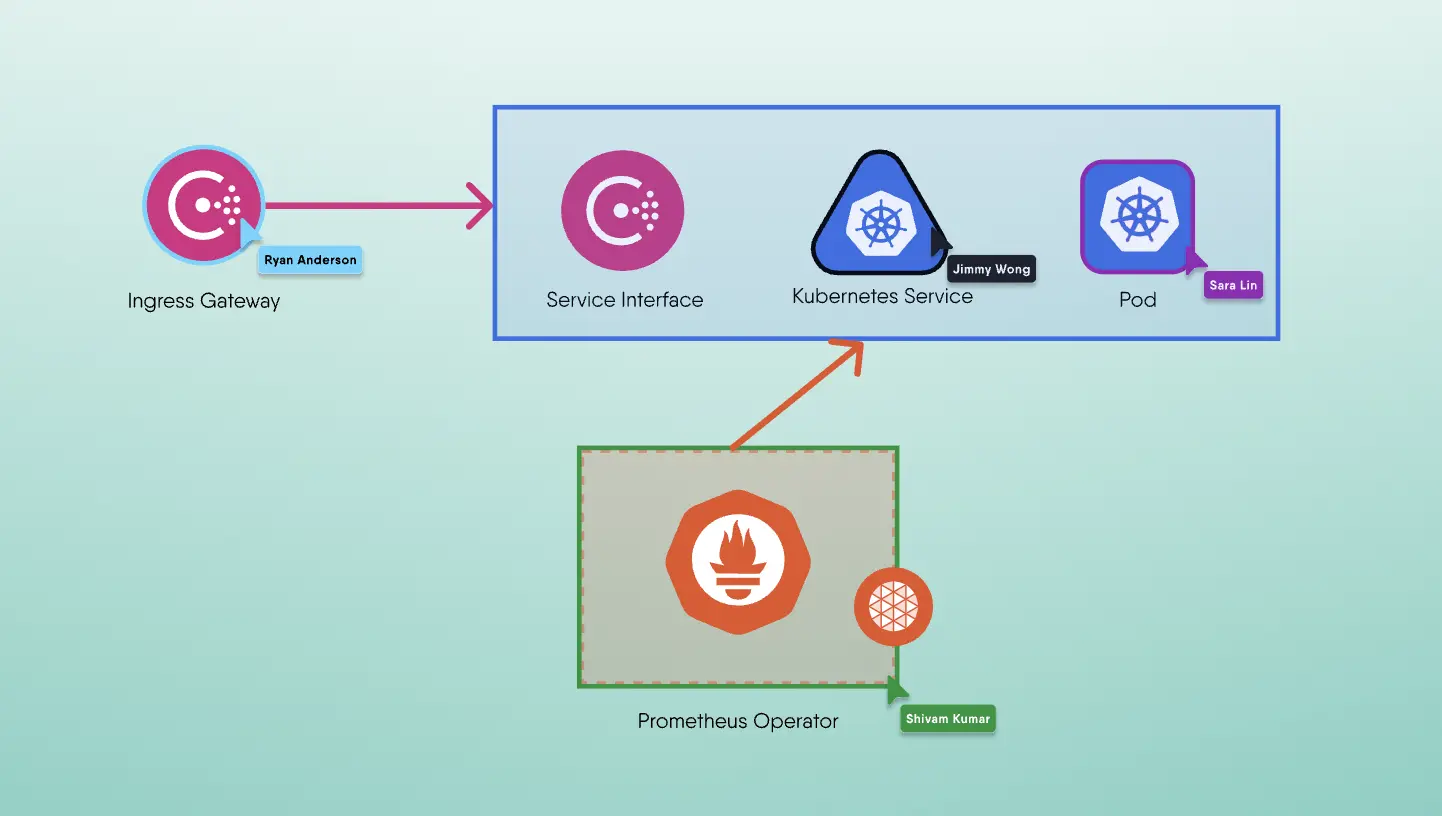
A data plane and a control plane are logically separate parts of an Istio service mesh.
- A group of intelligent proxies (Envoy) that are deployed as sidecars make up the data plane. All network connection among the microservices is mediated and managed by these proxies. Additionally, they gather and compile data on all mesh communications.
- The proxies are controlled and set up by the control plane to route traffic.
Envoy
The data plane of Istio consists of the Envoy sidecar proxy. Envoy is an edge and service proxy that is open source and free that aids in separating network concerns from core applications. Applications don't care about the network topology; they just transmit and receive messages to and from localhost. Envoy is fundamentally a network proxy that operates at the OSI model's L3 and L4 layers. It operates by processing connections through a series of pluggable network filters. Envoy additionally provides support for an extra L7 layer filter for HTTP-based traffic. Envoy also offers excellent support for the HTTP/2 and gRPC transports.
Many of the features provided by Istio such as security, traffic control, network resiliency are possible due to Envoy.
Istiod
Service discovery, configuration, and certificate management are offered by Istiod.
High level routing rules that govern traffic behavior are transformed into Envoy-specific configurations by Istiod and propagated to the sidecars during runtime. Any sidecar that complies with the Envoy API can use Pilot, which synthesizes platform-specific service discovery techniques into an abstract form.
Istio can handle discovery in a variety of settings, including Kubernetes or virtual machines.
To exert finer control over the traffic in your service mesh, you can ask Istiod to modify the Envoy configuration using the Traffic Management API.
Strong service-to-service and end-user authentication are made possible by Istiod security's integrated identity and credential management. Istio can be used to enhance unencrypted service mesh traffic.
Operators can enforce regulations with Istio based on service identity rather than on layer 3 or layer 4 network IDs, which are more prone to instability. Additionally, you can limit who has access to your services by using Istio's authorisation capability.
In order to enable secure mTLS connection in the data plane, Istiod performs the role of a Certificate Authority (CA) and issues certificates.
Features
Traffic Management
Performance is impacted by traffic routing, both within and across clusters, which improves deployment strategy. You can simply manage the flow of traffic and API requests between services using Istio's traffic routing rules. Istio makes it simple to configure critical activities like A/B testing, canary deployments, and staged rollouts with percentage-based traffic divides, as well as service-level attributes like circuit breakers, timeouts, and retries.
Observability
It becomes harder to comprehend behaviour and performance as services become more complicated. Istio produces comprehensive telemetry for each communication taking place within a service mesh. This telemetry makes service activity observable, enabling operators to maintain, optimise, and debug their applications. Even better, you can implement practically all of this instrumentation without making any changes to your applications. Operators are able to fully comprehend how the monitored services are communicating with Istio.
Detailed metrics, distributed traces, and complete access logs are all included in Istio's telemetry. You get complete and thorough service mesh observability with Istio.
Security Capabilities
Particular security requirements for microservices include defense against man-in-the-middle attacks, adaptable access rules, auditing tools, and mutual TLS. Istio comes with a comprehensive security solution that enables administrators to handle each of these problems. To safeguard your services and data, it offers strong identity, strong policy, transparent TLS encryption, and authentication, authorization, and audit (AAA) tools.
The security architecture used by Istio is built on security-by-default, and it aims to provide in-depth defense so you may deploy security-conscious apps even across networks with a low level of trust.